Join us on our quest to rule the galaxy.
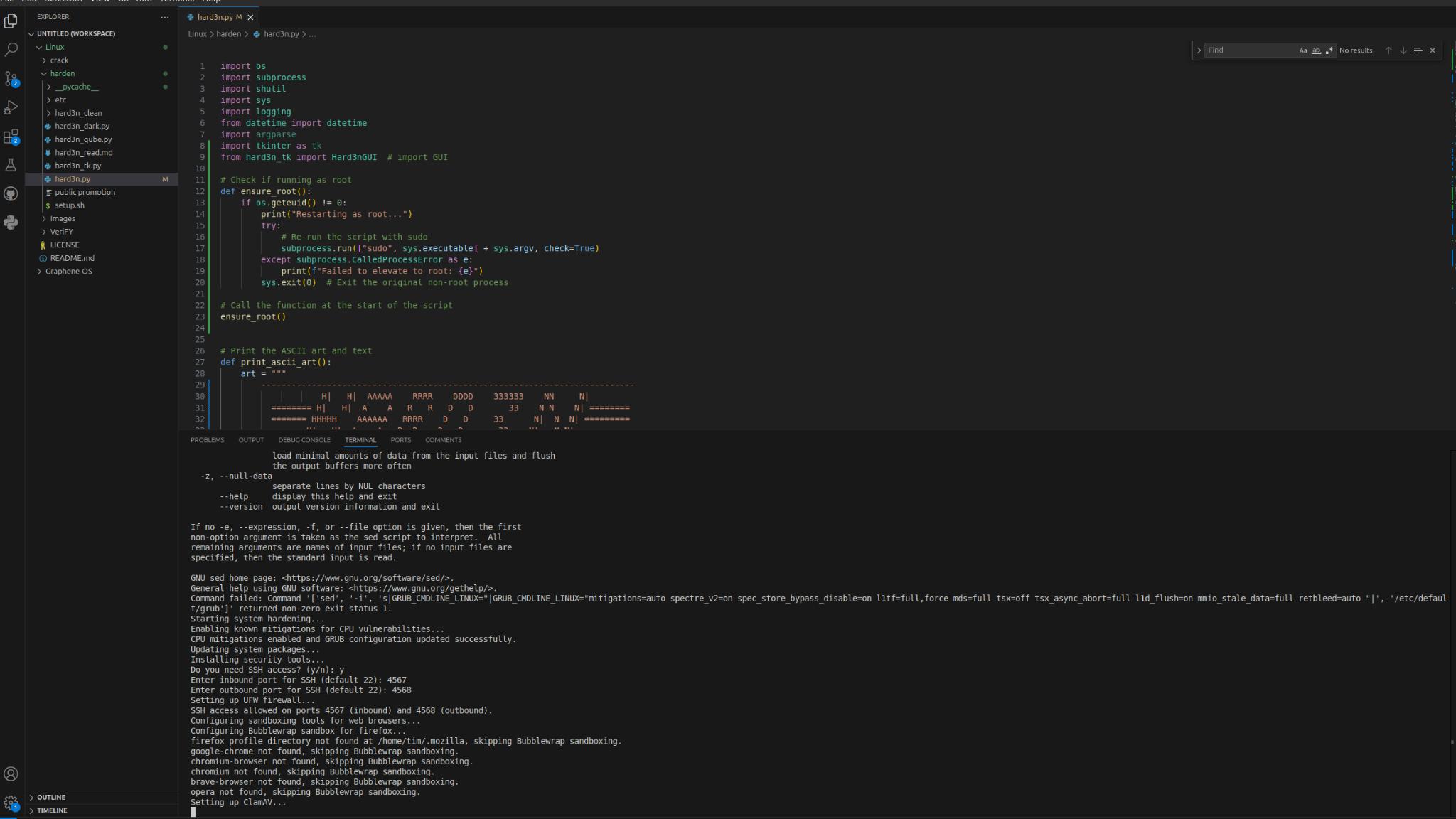
1. Go here:
https://cdimage.debian.org/debian-cd/current/amd64/iso-dvd/
2. Download the latest Debian ISO image.
3. Create a VM in VirtualBox using the above ISO.
4. Power on your new VM (must have 8 GB of RAM on that VM).
5. Add your user to sudoers with the command: sudo usermod -aG sudo username
Install software packages using the command: apt install git btop htop build-essential
6. Reboot your VM
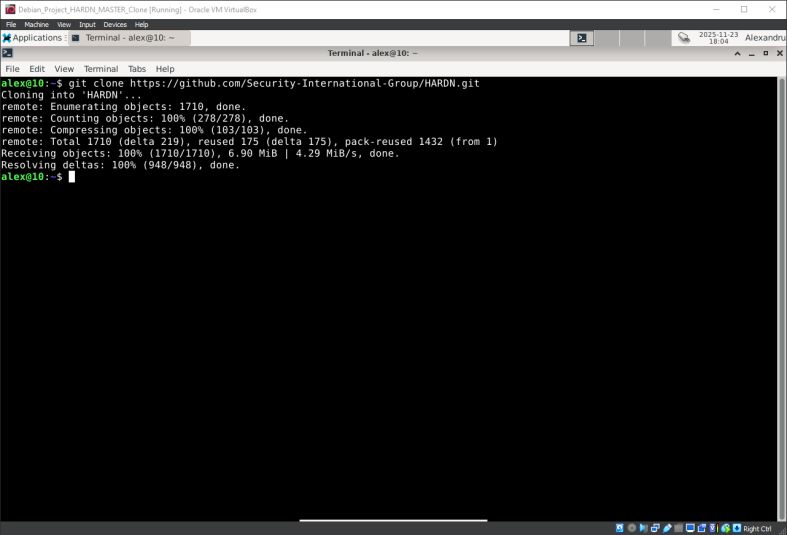
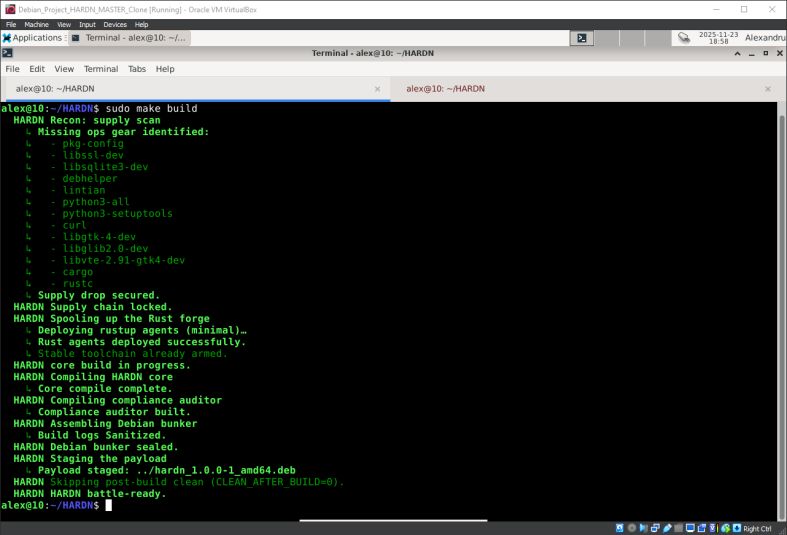
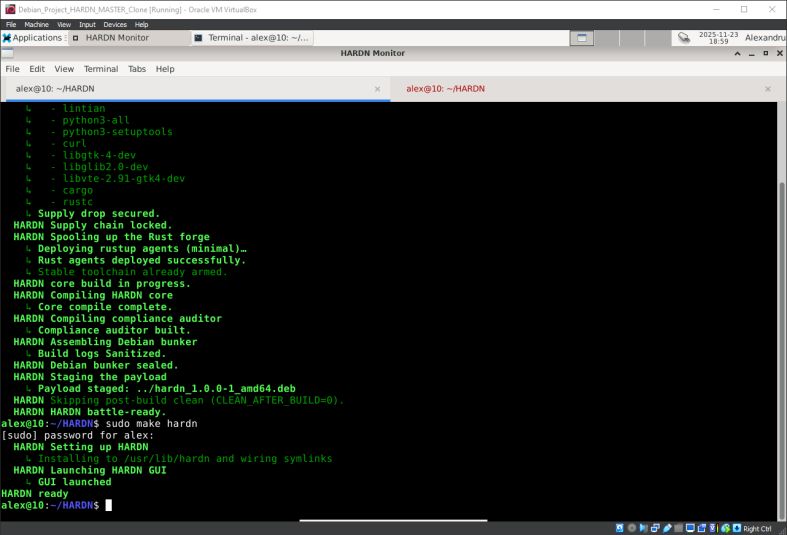
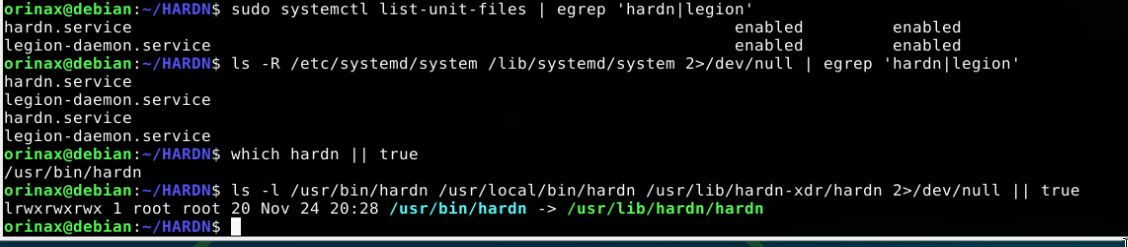
7. Run these commands:
git clone https://github.com/Security-International-Group/HARDN
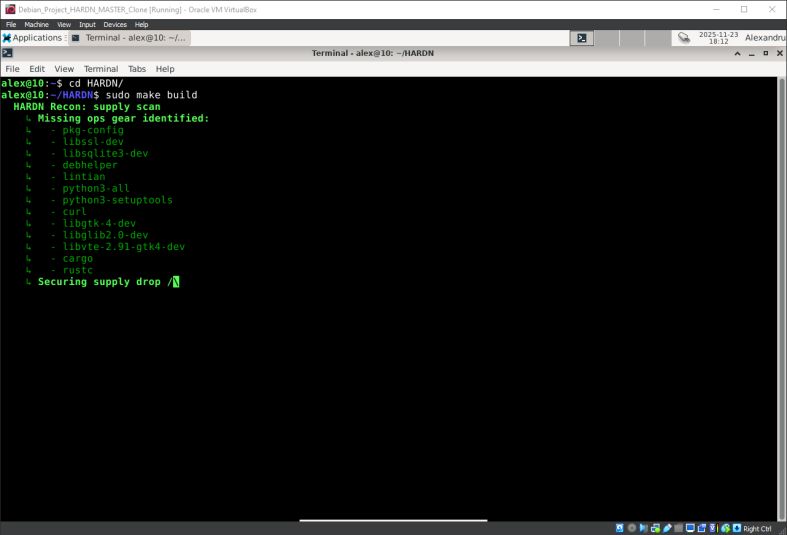
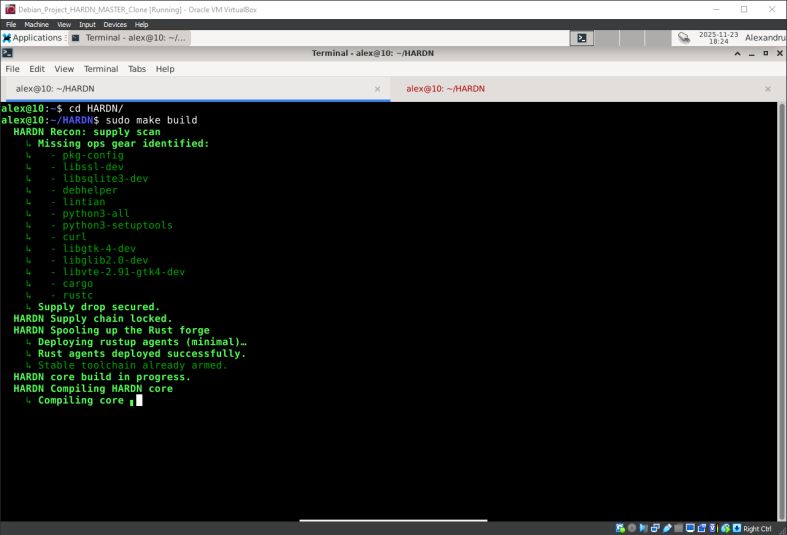
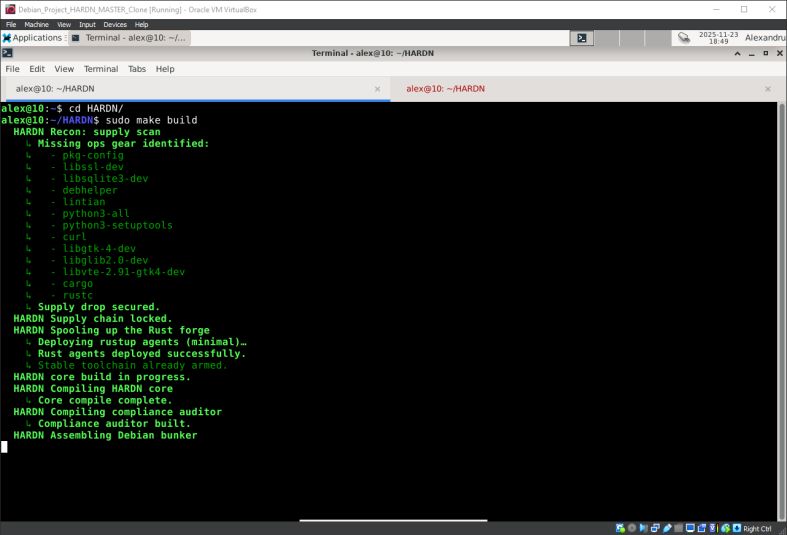
cd HARDN
sudo make build
sudo make hardn
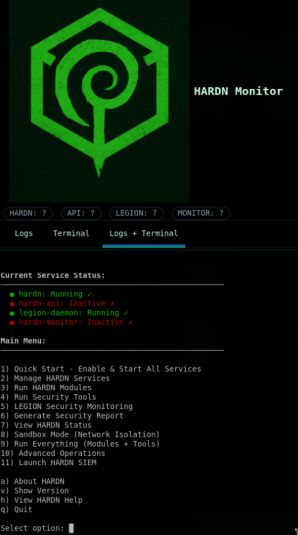
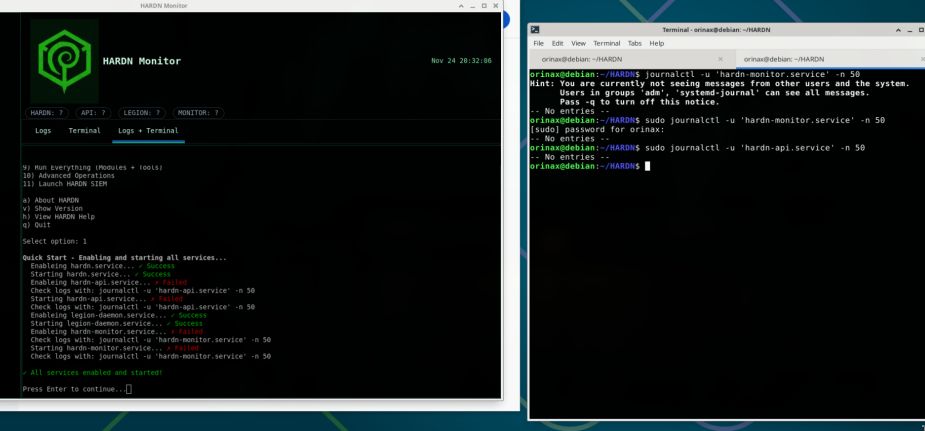
8. Enjoy the magic
DO NOT RUN THIS DIRECTLY ON YOUR LINUX MACHINES!
VM only; this is experimental and prone to failure.
Enjoy #linux and don`t forget to donate
Get yours here:
https://github.com/Security-International-Group/HARDN

Long live our Project HARDN
Had an amazing trip to the 2025 GitHub Universe
Had an amazing trip to the 2025 GitHub Universe, digging into where Agentic DevOps is headed. The shift toward AI->driven pipelines, self-healing workflows, and autonomous code/runtime checks is moving fast, and it’s clear this will become the backbone of how modern engineering teams build, secure, and ship.
Great conversations around: Agent-assisted CI/CD orchestrationSecure-by-default automationReal-time code understanding + remediationScaling developer impact without scaling burnout Excited to bring these ideas back into our ecosystem and continue pushing toward a fully integrated, intelligent DevSecOps model.
Enjoy #linux
Get yours here:
https://securityinternationalgroup.org/

HARDN — Frequently Asked Questions
Welcome to the official HARDN FAQ by Security International Group (SIG)
Below are answers to common questions about the project, usage, and contribution.
What is HARDN?
HARDN (Hardened Automation for Redundant Defense Networks) is an open-source Linux hardening framework that automates STIG, CIS, and FedRAMP compliance for secure systems.
Who maintains HARDN?
Maintained by Security International Group, a cybersecurity collective focused on automation, compliance, and open-source defense.
What platforms are supported?
Debian-based Linux systems are fully supported.
Is HARDN open source?
Yes — all code is publicly available on GitHub.
Repository:
https://github.com/Security-International-Group/HARDNHow can I contribute?
Submit issues, pull requests, or feature ideas on GitHub following SIG’s contribution standards.
What standards does HARDN implement?
HARDN implements DISA STIG standards and aligns with CIS Benchmarks, integrating internal compliance checks to ensure robust and verifiable system security.
What makes HARDN different?
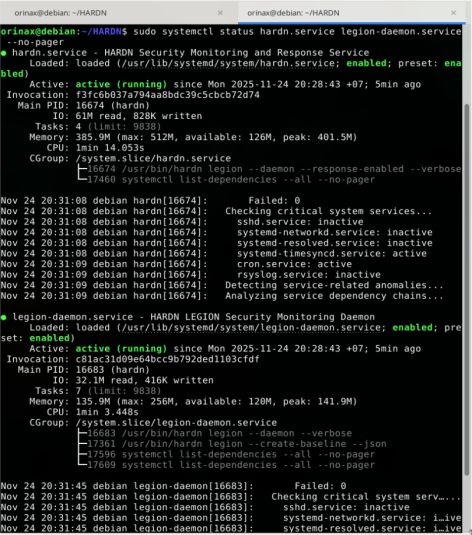
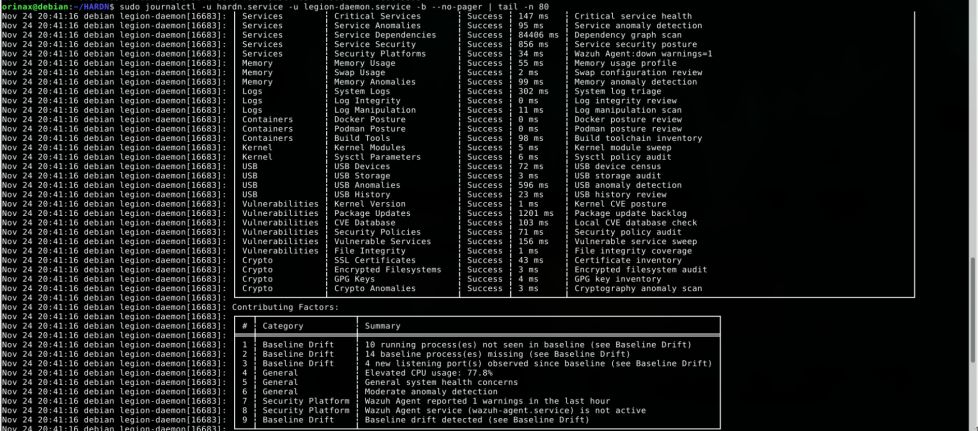
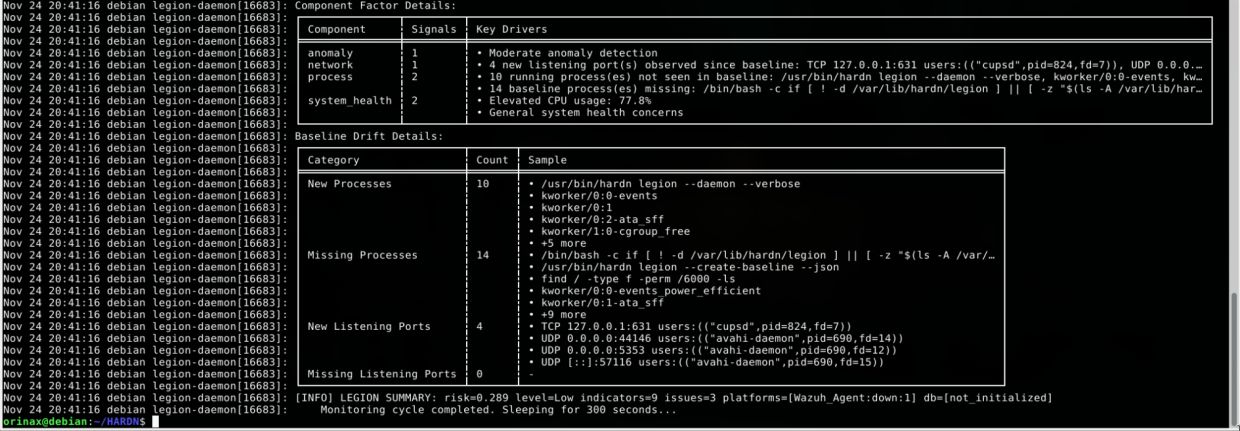
HARDN combines automation, telemetry, and continuous compliance verification through its LEGION daemon, SIEM dashboard, and service manager, delivering active system hardening rather than one-time configuration.
How do I get support or report bugs?
Open a support ticket in Discord (#support) or report directly on GitHub.
Can I use HARDN commercially?
Yes — it’s open source and may be used or integrated under its license.
Learn more
Visit the official site:
https://securityinternationalgroup.org/© 2025 Security International Group | HARDN
Thank you Alexis Soto-Yanez
https://www.linkedin.com/in/alexis-sotoyanez/You are an excellent team player!
Our Project HARDN official website is up and running!
We used to host it with me at Cyber Synapse but now we finally have our own independent project server.
Enjoy #linux 🐧 and don't forget to generously donate
Long live the open source community projects!
Yes, there will be a commercial product in the future but for now we have our demo version completely free for everyone!
And, we do need unpaid volunteer QA to help us with our project.
Write to me if you wish to join our team.
Join the community
Visit Our Project HARDN official website here:
https://securityinternationalgroup.org/

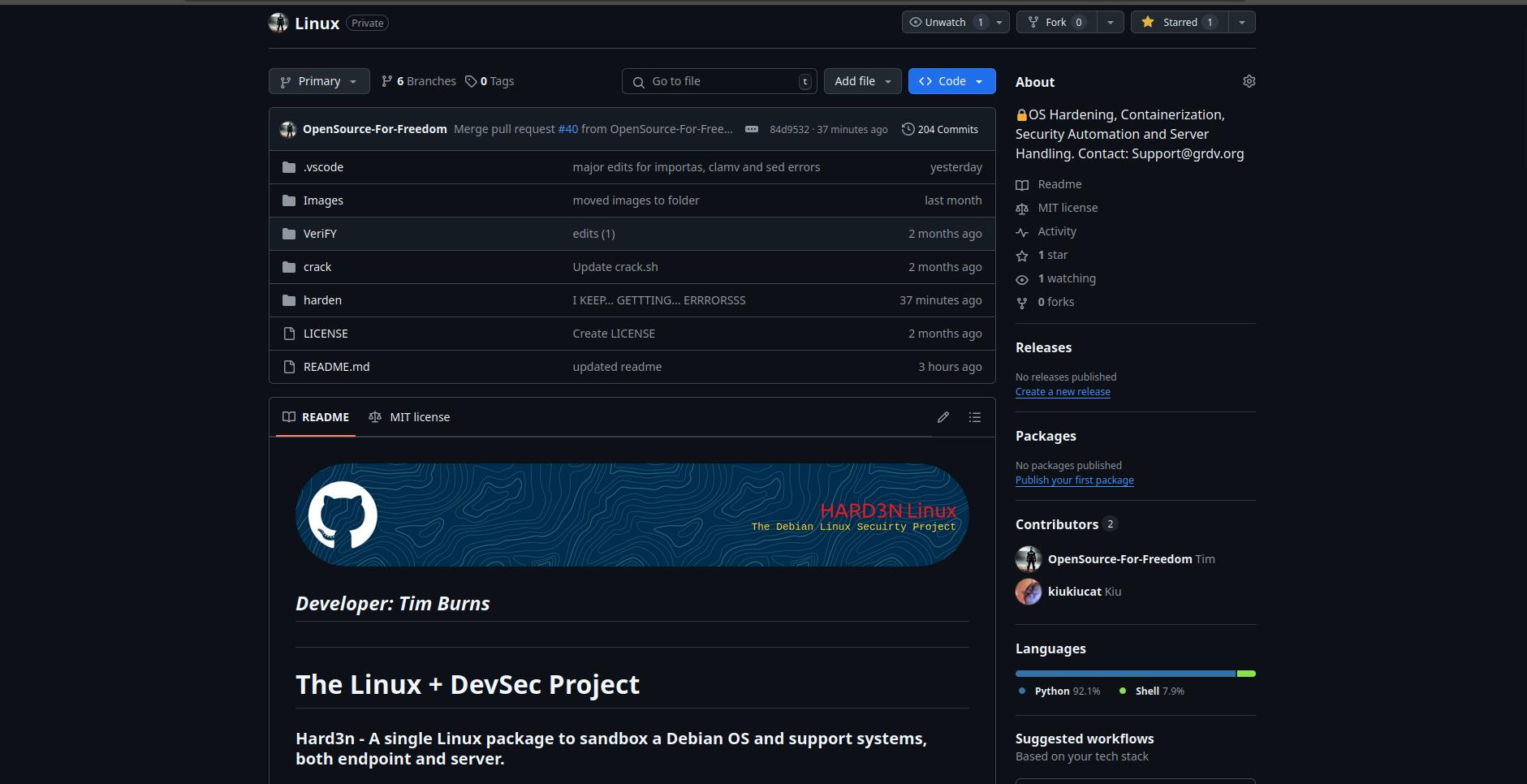
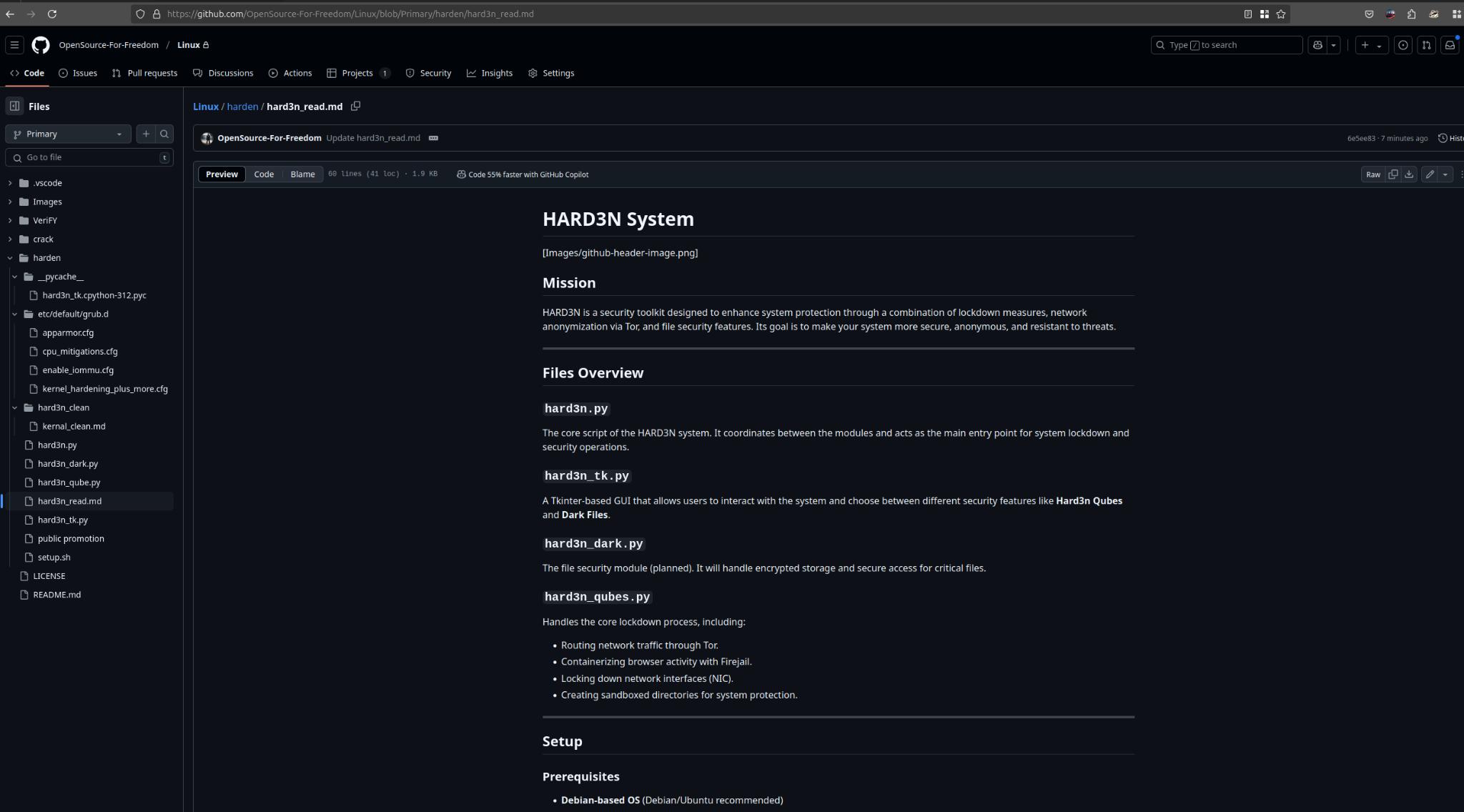
Insights into HARDN – The Linux Security Project
A Comprehensive Debian Hardening Repository and Mission
GitHub
https://github.com/OpenSource-For-Freedom
Abstract
The HARDN Linux project is an open-source effort aimed at making Debian Linux systems more secure and efficient.
With a focus on modular design and automation, it uses research-driven methods to strengthen system defenses, fix vulnerabilities, and boost performance.
This write-up takes a closer look at the project’s structure, goals, and how it’s being implemented, offering insights into the steps being taken before its official release and what it means for Linux security.
Introduction
Securing Linux systems is a crucial part of modern computing, especially for Debian-based distributions.
The HARDN – Linux project brings together tried-and-true security practices with automation, creating a user-friendly yet powerful toolkit for protecting Linux environments.
The project focuses on strengthening security through careful permission management, well-crafted security policies, and the use of reliable tools.
With its commitment to transparency and collaboration, the HARDN – Linux Project is a valuable resource for Linux administrators and cybersecurity experts alike.
Repository Structure
Core Directories and Scripts
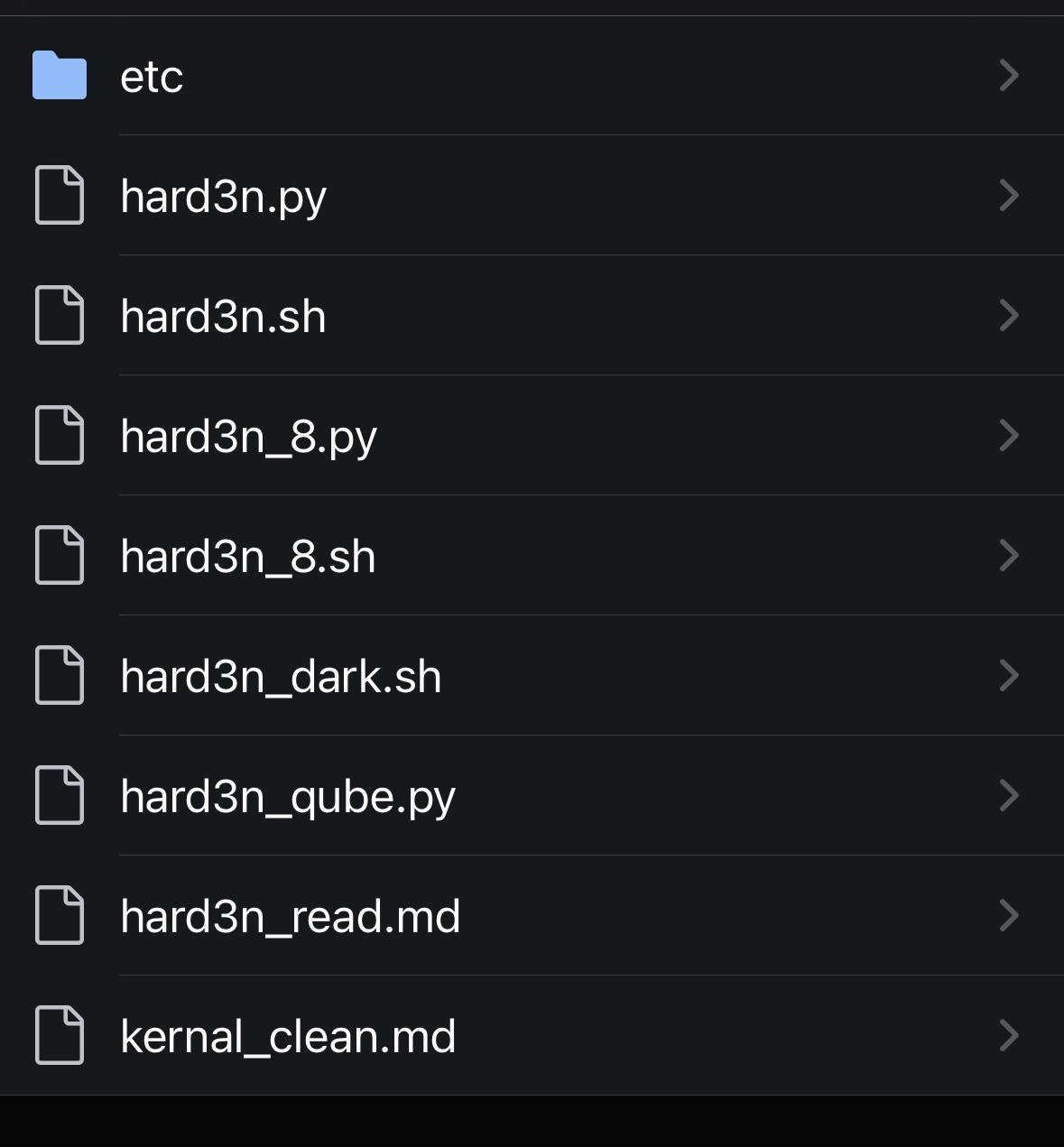
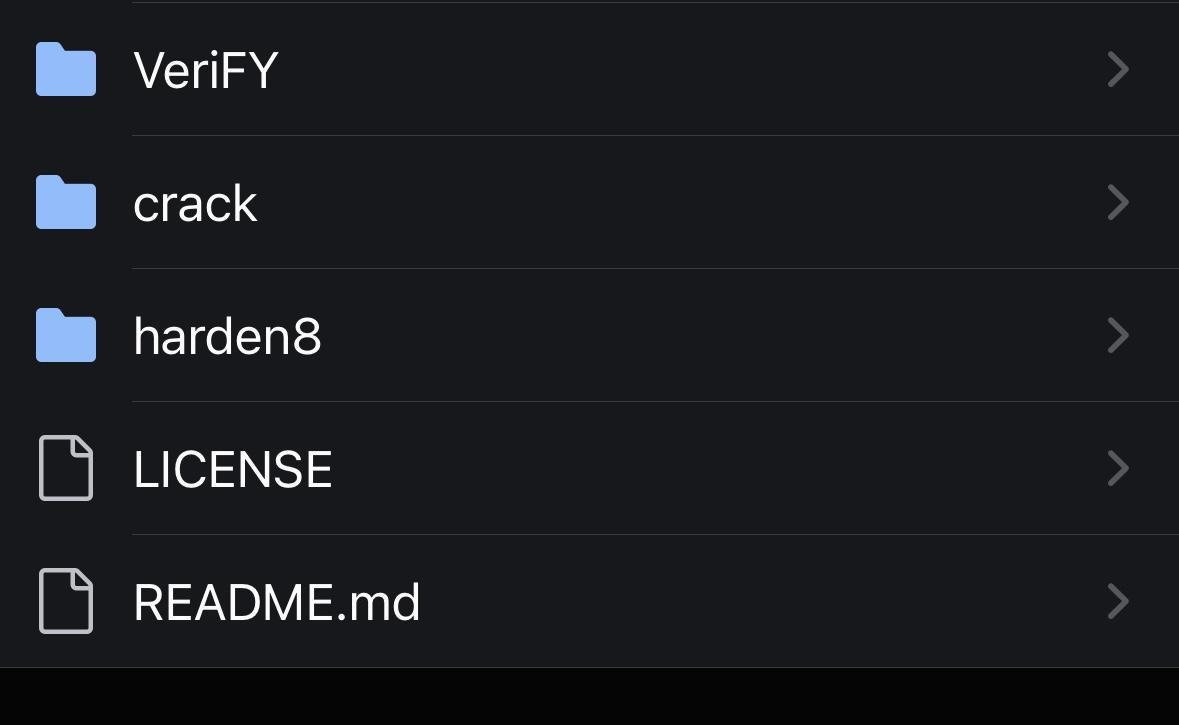
The HARDN – Linux repository features the following components:
1. HARDN Project Scripts
• Project.py: Python scripts automating critical hardening tasks.
• Project_dark.sh: Dependant Shell scripts for additional security features tailored for Debian systems.
• Project_qube.py: A specialized script, possibly designed for virtualized environments or containerized security configurations similar to Qubes Linux OS.
2. Documentation
• read.md and kernal_clean.md: Comprehensive guides detailing the hardening process, kernel optimization, and system configuration adjustments.
3. Critical Research and Configuration Files
• The etc directory houses custom configuration files, including advanced security settings for the /etc directory.
Key Objectives of HARDN
The primary aim of HARDN is to deliver a fortified, performance-optimized Debian system. The following objectives outline its focus:
1. System Hardening Research
• Objective: Understand and adapt successful hardening strategies, such as those used in Harbian Audit and similar projects.
• Approach: Study the structure and logic of existing security measures to adopt best practices for vulnerability mitigation.
• Outcome: Comprehensive hardening tailored specifically for Debian systems.
2. Permission Security
• Objective: Evaluate and safely modify sensitive permissions (e.g., setuid and setgid) to minimize attack surfaces.
• Implementation Example:
find / -mount -perm -2000 -type f -exec ls -ld {} \; > /home/user/setgid_.txt && chown -v user:user /home/user/setgid_.txt
This command identifies files with elevated group permissions for further review and adjustment.
3. User Group Configuration
• Objective: Optimize user group configurations to prevent privilege escalation.
• Implementation: Inspired by systems like Whonix, investigate the necessity of specific groups and explore additional security improvements.
4. Security Enhancements
• Modify critical configuration files (/etc/security, /etc/host.conf) to:
• Tighten password policies.(72 day enforcement)
• Restrict sudo access.
• Configure account lockouts after repeated failed login attempts.
• Secure bootloader and update mechanisms.
Pre-Release Activities
The repository meticulously outlines pre-release steps to ensure a secure and efficient system, including:
1. Log Auditing and Monitoring
• Enable detailed logging configurations.
• Automate log analysis for suspicious activity detection. /var/dev/sbin/root directories
2. Backup and Recovery Planning
• Establish reliable strategies for system and data recovery.
3. Controlled Testing
• Validate all security measures in a staging environment to identify and resolve issues before release.
4. Documentation
• Maintain thorough documentation for all hardening processes to facilitate transparency and future updates.
Tools and Frameworks Implemented
The HARDN project integrates several state-of-the-art tools to enhance system security:
1. Lynis:
• A security auditing tool for Unix-based systems that identifies vulnerabilities and misconfigurations, providing actionable recommendations for hardening.
2. Fail2Ban:
• Protects against brute-force attacks by monitoring login attempts and dynamically banning malicious IPs through firewall rules.
3. UFW (Uncomplicated Firewall):
• A simplified firewall management tool for configuring rules that restrict unauthorized access to system resources.
4. AppArmor:
• Enforces security policies through Mandatory Access Control (MAC), restricting applications to predefined actions based on their assigned profile.
5. Firejail:
• A lightweight sandboxing tool that isolates applications, limiting their ability to access critical system resources and reducing the risk of privilege escalation.
6. ClamAV:
• An open-source antivirus solution designed to detect and remove malware, including viruses, Trojans, and other malicious software, from Linux systems.
7. Modprobe:
• What It Does: Modprobe is a critical tool for managing kernel modules in Linux. It allows administrators to dynamically load, unload, or blacklist modules.
8. Importance in Hardening:
• Misconfigured or unnecessary kernel modules can introduce vulnerabilities, such as enabling unused hardware drivers or insecure protocols.
• Hardening involves blacklisting unnecessary or insecure modules, like usb_storage, which might expose the system to attacks such as unauthorized data exfiltration.
• Example Use in Hardening:
To blacklist a module (e.g., usb_storage), create a blacklist configuration file:
echo "blacklist usb_storage" >> /etc/modprobe.d/blacklist.conf
This prevents the module from being loaded into the kernel, reducing potential attack surfaces.
• Additional Configurations:
Modprobe can also be used to enforce parameters for allowed modules, ensuring they operate within strict security guidelines.
Conclusion and Next Steps
The HARDN project is a robust effort aimed at fortifying Debian Linux systems against a wide range of security threats.
By automating and streamlining system hardening tasks, it simplifies the implementation of advanced security measures.
The repository’s detailed roadmap, comprehensive testing procedures, and use of best-in-class tools make it an invaluable resource for Linux security professionals.
Next Steps:
• Enhance the scope of automation for hardening and monitoring tasks.
• Look to partner with Tailscale for a comprehensive exit node VPN IPsec (P2P) for server hosted systems.
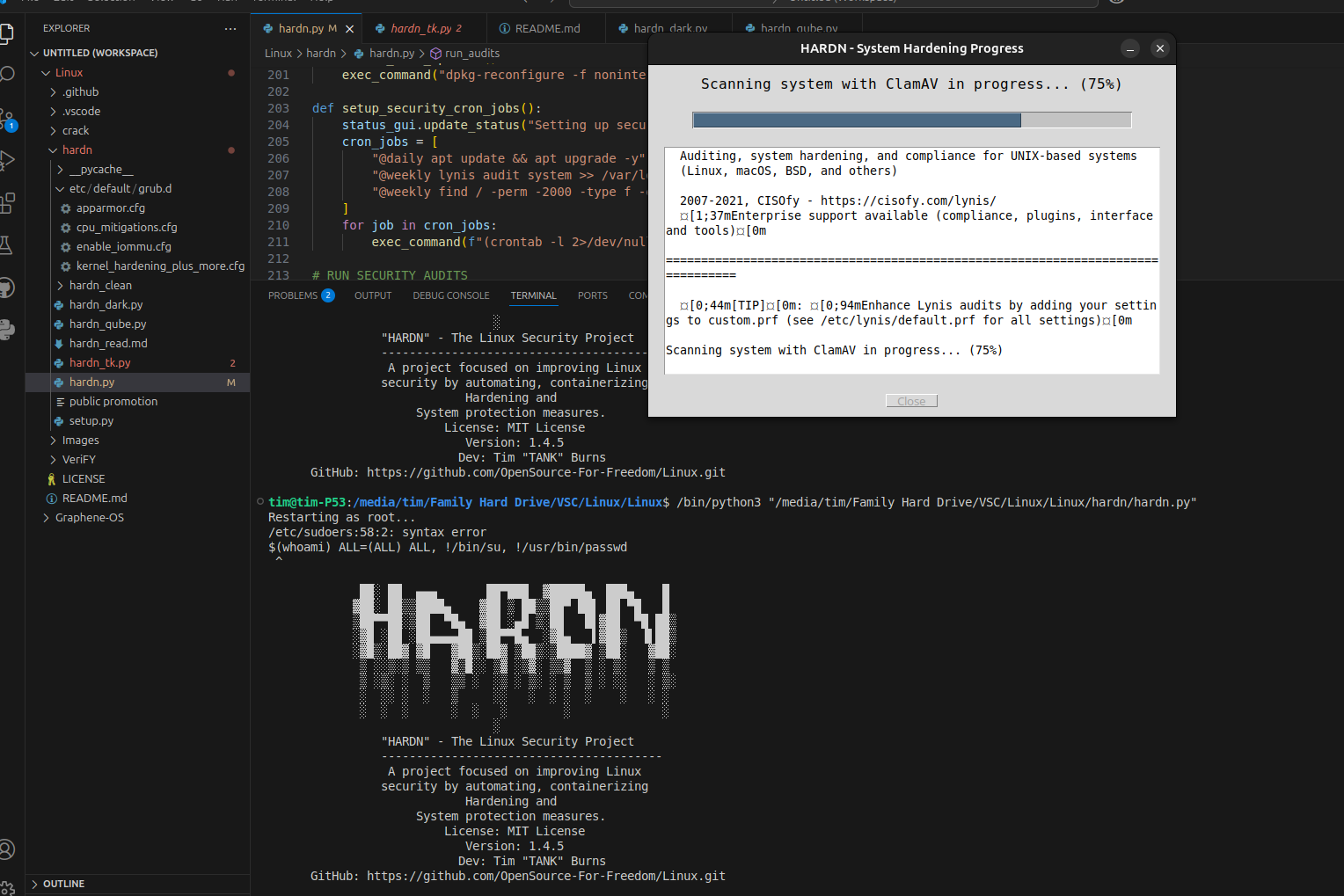
• including crontab and tkinter (python gui)
• Incorporate additional tools such as SELinux for advanced access control.
• Expand testing frameworks to cover diverse deployment scenarios.
• Finalize documentation for user-friendly deployment and customization.
Project Progress Update
Internally version 1.0 has been completed and verified/validated by our team.
---------------------------------------------------------------------
Work has progressed to version 1.3 internally and now version 1.4 is the targeted final version.
---------------------------------------------------------------------
Perhaps version 1.4 can be released publically in the summer of 2025.
Furthermore, work has progressed well using the private GitHub repository as we have felt the work was not yet fully ready for public scrutiny.
---------------------------------------------------------------------
Nevertheless, there have been some exciting developments:
• We have fully integrated ClamAV into our cybersecurity solution
• We have started work on our in-house development Linux Malware Scanner.
---------------------------------------------------------------------
The second feature was not planned for initially but we are excited to delve into this new feature as we felt during internal testing that ClamAV is a bit dense and slow during scanning and we needed a faster solution.
Fully integrated in our project, a scan of about 300 GB of data on a Linux machine using ClamAV took hours and did not provide the adequate performance we has initially envisioned and hoped for.
It fully occupied the CPU on our test machine and prevented it work working productively as a server should.
We deemed this situation unacceptable and began work on our secondary option to offer our users: a new in-house Linux-only malware scanner.
This code we managed to code the first prototype version to help us figure out the ins and outs of such a technology.
Performance has improved.
We rely of 5 different databases for the threat signatures, for now.
This new feature is very much experimental and we do need time to work out the best technique to get fast performance, low CPU usage and deep efficient malware scanning.
The more threat signature databases it relies on during scanning, the slower it becomes and the denser.
This will increase the CPU usage to an unacceptable high level.
Other cybersecurity vendors have demonstrated their ability to create an efficient smart scan function that prevents the above scenario.
We aim to do the same and are actively working on it.
---------------------------------------------------------------------
The final goal of this project is to gather support and a community around us to create a fully capable cybersecurity solution that would be directly comparable in terms of features and performance to what commercial vendors are now offering for money.
But we would offer it for free.
Open source freedom.
---------------------------------------------------------------------
We are also looking to package this as a true Debian Linux package that you would install by calling apt from the command line and download it from the official repository servers.
Of course, this requires validation from the Debian development community and we still have a long way to go before we get there but, we are keen on that future goal.
---------------------------------------------------------------------
We are calling on Linux Engineers, Admins and Users to keep an eye on our project and first release (we hope for next summer).
We will need lots of users to test out our solution and iron out any potential issues.
To keep this project alive, past the first future public release, we will need you.
---------------------------------------------------------------------
In all honesty, the core goals of the initial project have already been fulfilled.
HARDN works perfectly, aside the malware / viral scanner and feature.
This matter is being addressed even as you are reading this.
And, most importantly, we can confirm integration with Wazuh.
---------------------------------------------------------------------
What is the next step?
• Get the Linux Malware Scanner fully prepped.
• We need to build a threat signature, light weight malware scanner that updates daily pulling from 5 separate URL resources, and just looks for anomalies and watches signatures.
• Create a LLM that learns and detects and builds a response Yara rule and can pivote.
• Get it out there to the public by summer 2025.
A few preview bits

Thought of the day
“Every decision has a consequence, not choosing to move is still a choice, and staying in place also comes at a cost”
We can build anything… we are not limited by anything or anyone.
Long live Open Source!
If you wish to support our project
Donation link (Buy me a coffee):
https://buymeacoffee.com/Alex_Cyber_Synapse
HARDN – The Linux Security Project stands as a testament to the power of open-source collaboration, emphasizing the importance of system hardening in an era of increasing cybersecurity threats.
Hold fast, this will be public soon after initial testing and restructuring!
